Advertisement
Information gathering can be broken into seven logical steps. Footprinting is performed during the first two steps of unearthing initial information and locating the network range.
Footprinting
Footprinting is defined as the process of establishing a scenario or creating a map of an organization's network and systems. Information gathering is also known as footprinting an organization. Footprinting is an important part of reconnaissance process which is typically used for collecting possible information about a targeted computer system or network. Active and Passive both could be Footprinting. The example of passive footprinting is assessment of a company's website, whereas attempting to gain access to sensitive information through social engineering is an example of active information gathering. Basically footprinting is the beginning step of hacker to get hacked someone because having information about targeted computer system is the main aspect of hacking. If you have an information about individual you wanna hack so you can easily hacked that individual. The basic purpose of information gathering is at least decide what type of attacks will be more suitable for the target. Here are some of the pieces of information to be gathered about a targetduring footprinting:
- Domain name
- Network blocks
- Network services and applications
- System architecture
- Intrusion detection system
- Authentication mechanisms
- Specific IP addresses
- Access control mechanisms
- Phone numbers
- Contact addresses
Footprinting Tools
Footprinting can be done using hacking tools, either applications or websites, which allow the hacker to locate information passively. By using these footprinting tools, a hacker can gain some basic information on, or "footprint," the target. By first footprinting the target, a hacker can eliminate tools that will not work against the target systems or network. For example, if a graphics design firm uses all Macintosh computers, then all hacking software that targets Windows systems can be eliminated. Footprinting not only speeds up the hacking process by eliminating certain tool sets but also minimizes the chance of detection as fewer hacking attempts can be made by using the right tool for the job. Some of the common tools used for footprinting and information gathering are as follows:- Domain name lookup
- Whois
- NSlookup
- Sam Spade
Footprinting a Target
Footprinting is part of the preparatory pre-attack phase and involves accumulating data regarding a target's environment and architecture, usually for the purpose of finding ways to intrude into that environment. Footprinting can reveal system vulnerabilities and identify the ease with which they can be exploited. This is the easiest way for hackers to gather information about computer systems and the companies they belong to. The purpose of this preparatory phase is to learn as much as you can about a system, its remote access capabilities, its ports and services, and any specific aspects of its security.DNS Enumeration
DNS enumeration is the process of locating all the DNS servers and their corresponding records for an organization. A company may have both internal and external DNS servers that can yield information such as usernames, computer names, and IP addresses of potential target systems.NSlookup and DNSstuff
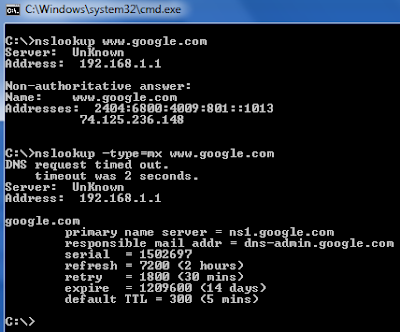
One powerful tool you should be familiar with is NSlookup (see Figure 2.2). This tool queries DNS servers for record information. It's included in Unix, Linux, and Windows operating systems. Hacking tools such as Sam Spade also include NSlookup tools. Building on the information gathered from Whois, you can use NSlookup to find additional IP addresses for servers and other hosts. Using the authoritative name server information from Whois ( AUTH1.NS.NYI.NET ), you can discover the IP address of the mail server.Syntax
nslookup www.sitename.com
nslookup www.usociety4.com
 |
| Performing DNS Lookup |
Understanding Whois and ARIN Lookups
Whois evolved from the Unix operating system, but it can now be found in many operating systems as well as in hacking toolkits and on the Internet. This tool identifies who has registered domain names used for email or websites. A uniform resource locator (URL), such as www.Microsoft.com , contains the domain name ( Microsoft.com ) and a hostname or alias ( www ).The Internet Corporation for Assigned Names and Numbers (ICANN) requires registration of domain names to ensure that only a single company uses a specific domain name. The Whois tool queries the registration database to retrieve contact information about the individual or organization that holds a domain registration.
Using Whois
- Go to the DNSStuff.com website and scroll down to the free tools at the bottom of the page.
- Enter your target company URL in the WHOIS Lookup field and click the WHOIS button.
- Examine the results and determine the following:
- Registered address
- Technical and DNS contacts
- Contact email
- Contact phone number
- Expiration date
- Visit the company website and see if the contact information from WHOIS matches up to any contact names, addresses, and email addresses listed on the website.
- If so, use Google to search on the employee names or email addresses. You can learn the email naming convention used by the organization, and whether there is any information that should not be publicly available.
Syntax
whois sitename.com
whois usociety4.com
Read more
- Pentest Tools Alternative
- Hacking Tools Github
- Pentest Tools For Windows
- Hacking Apps
- Hack Apps
- Pentest Tools For Mac
- Hacking Tools Download
- Pentest Tools Online
- Hacking Tools For Windows Free Download
- Pentest Tools Android
- Pentest Tools Free
- Pentest Tools Tcp Port Scanner
- Hacker Tools For Ios
- Pentest Tools Website Vulnerability
- Hacker
- Hack Tool Apk No Root
- New Hacker Tools
- Hacker Tools List
- Hacker Tools For Mac
- Hacking App
- Hacking Tools For Games
- Android Hack Tools Github
- Hack Tools 2019
- Tools Used For Hacking
- Blackhat Hacker Tools
- Pentest Recon Tools
- Pentest Tools Tcp Port Scanner
- Hacker Tools 2020
- Pentest Tools For Windows
- Pentest Tools Port Scanner
- Kik Hack Tools
- Hacking Tools Usb
- Game Hacking
- Hack Tools Pc
- Hacking Tools Online
- Hacking Tools Github
- New Hacker Tools
- Hacking Tools For Mac
- Growth Hacker Tools
- New Hack Tools
- Pentest Tools Url Fuzzer
- Computer Hacker
- Hacker Tools
- Pentest Tools Nmap
- Hacking Tools 2019
- Hacker Tools For Windows
- Hack Tools Pc
- Tools For Hacker
- Hacker Tools Windows
- Hacker Security Tools
- Pentest Tools Free
- Physical Pentest Tools
- Hacking Tools Github
- Hacking Tools Pc
- Hacker Tools Hardware
- Hacking Tools Free Download
- Tools Used For Hacking
- Best Pentesting Tools 2018
- Hacking Tools And Software
- Hack Tools
- Pentest Tools Android
- Hacking Tools Download
- Hacker Tools
- Hacker Tools Free
- Pentest Recon Tools
- Hacking Tools Mac
- Hacker Tools List
- Game Hacking
- Hacker Tools Mac
- Hacking Tools Name
- Hacking Tools For Pc
- Tools Used For Hacking
- Hack Tool Apk No Root
- Hacker Tools For Pc
- Hack Tool Apk No Root
- Pentest Tools For Mac
- Hacker Tools Online
- Termux Hacking Tools 2019
- New Hacker Tools
- How To Install Pentest Tools In Ubuntu
- Hacking Tools For Pc
- Hack Apps
- Black Hat Hacker Tools
- Hacking Tools Windows 10
- Hacker Techniques Tools And Incident Handling
- Hacking Tools Mac
- Computer Hacker
- Hacker Tools Mac
- Hacker Tools For Pc
- Physical Pentest Tools
- Pentest Tools For Android
- Hack Tools For Mac
- Hack App
- Pentest Tools Tcp Port Scanner
- Physical Pentest Tools
- Hacker
- Easy Hack Tools
- Hack Tools For Mac
- World No 1 Hacker Software
- Easy Hack Tools
- Pentest Tools Port Scanner
- Hacker Tools Apk Download
- Hacking Tools Hardware
- Hack Tools Online
- Hack Rom Tools
- Hack Tools Mac
- Pentest Tools Subdomain
- Hacker Tools 2020
- Hacking Tools For Windows 7
- Pentest Tools Website
- Beginner Hacker Tools
- Hacking Tools For Games
- Pentest Tools For Ubuntu
- Hack Tools
- Hack And Tools
- Hack Tools Pc
- Hack Tools
- Hacking Tools For Windows
- Hacking Tools Windows 10
- Hack Tools
- Usb Pentest Tools
- Tools Used For Hacking
- Hacking Tools For Pc
- Hacker Tools
- What Is Hacking Tools
- Tools 4 Hack
- Pentest Reporting Tools
- Pentest Tools Open Source
- Hacking Tools 2019
- Tools Used For Hacking
- Best Hacking Tools 2019
- Install Pentest Tools Ubuntu
- Tools For Hacker
- Hacker Tools List
- Pentest Tools Windows
- Pentest Tools For Mac
- Pentest Tools Open Source
- Hacking Tools Name
- Hacker Tools Free Download
- Pentest Tools For Windows
- Hacking Tools Windows 10
- Hacker Tools 2019
- World No 1 Hacker Software
- Hack Tools For Pc
- Hack Tool Apk
- Hacks And Tools
- Hacking Tools For Windows Free Download
- Bluetooth Hacking Tools Kali
- Hacker
- Nsa Hack Tools Download
- Hacker Tools Free Download
- Pentest Tools Website Vulnerability
- Hacker Hardware Tools
- Hack Tools For Windows
- Hackrf Tools
- Hacking Tools For Mac
- Hacking Tools Software
- Hack And Tools
- Hacking Tools Name
- Hacking Tools Name


